Flutter抓包绕过
起因:
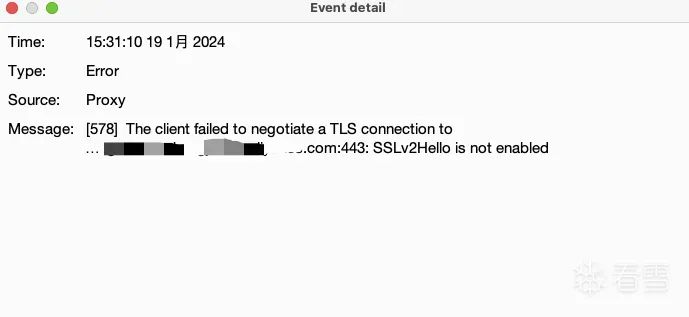
最近工作上让做个app的复测,把apk发我后,开始尝试挂代理抓包,结果发现抓不到。
以为是证书没弄好,想着前几天不是刚导入了吗(雾)。又重新导入了下还是不行。然后各种lsp模块,objection都不行,r0capture也没数据。
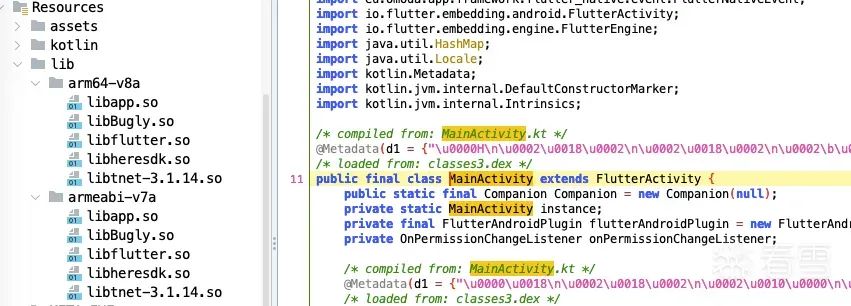
然后jadx看了下,全是flutter字样,才想起来和flutter有关。
然后就开始各种找,https://bbs.kanxue.com/thread-261941.htm
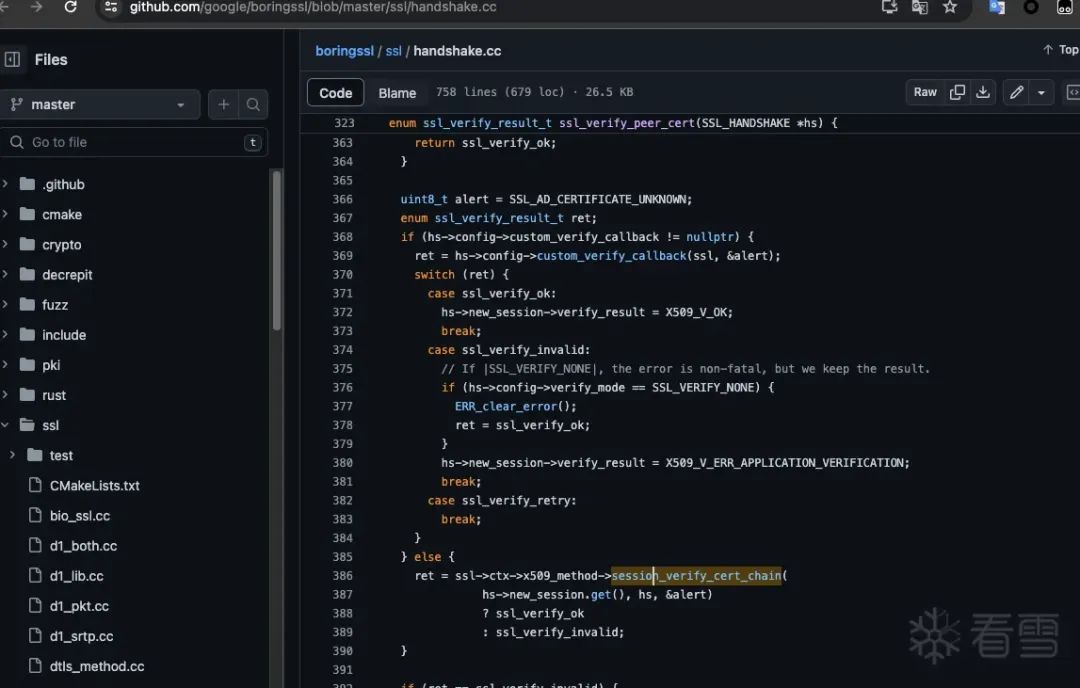
根据上面文章找到关键函数handshake.cc(https://github.com/google/boringssl/blob/master/ssl/handshake.cc)386行:
session_verify_cert_chain函数在第356行的ssl_x509.cc(https://github.com/google/boringssl/blob/master/ssl/ssl_x509.cc)中被定义:
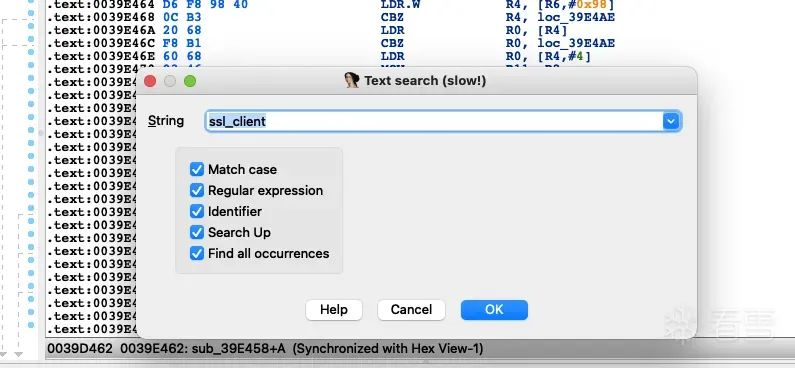
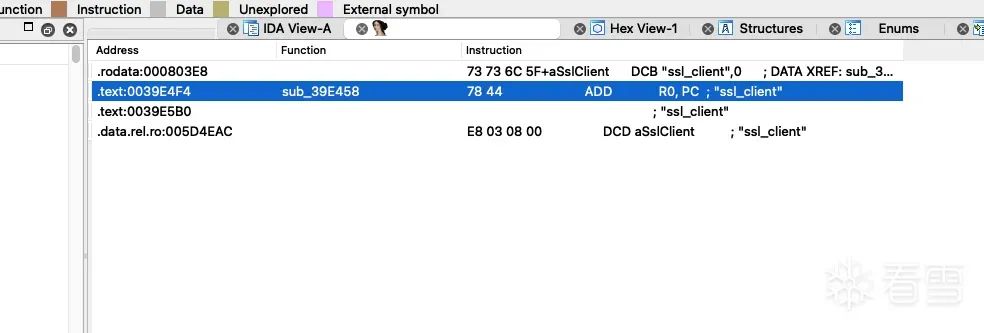
然后根据https://bbs.kanxue.com/thread-261941.htm这篇文章特征找,但是这个是32位的,所以在app安装的时候指定32位安装。
adb install --abi armeabi-v7a <path to apk>接下来就是找:
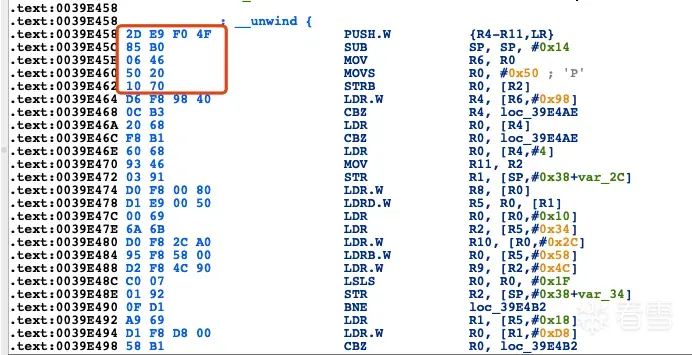
往上翻找:
2 写脚本绕过
32位
function hook_ssl_verify_result(address) {
Interceptor.attach(address, {
onEnter: function(args) {
console.log("Disabling SSL validation")
},
onLeave: function(retval) {
console.log("Retval: " + retval);
retval.replace(0x1);
}
});
}
function hookFlutter() {
var m = Process.findModuleByName("libflutter.so");
var pattern = "2D E9 F0 4F 85 B0 06 46 50 20 10 70";
var res = Memory.scan(m.base, m.size, pattern, {
onMatch: function(address, size){
console.log('[+] ssl_verify_result found at: ' + address.toString());
// Add 0x01 because it's a THUMB function
// Otherwise, we would get 'Error: unable to intercept function at 0x9906f8ac; please file a bug'
hook_ssl_verify_result(address.add(0x01));
},
onError: function(reason){
console.log('[!] There was an error scanning memory');
},
onComplete: function() {
console.log("All done")
}
});
}然后启动就可以抓包了:
64位
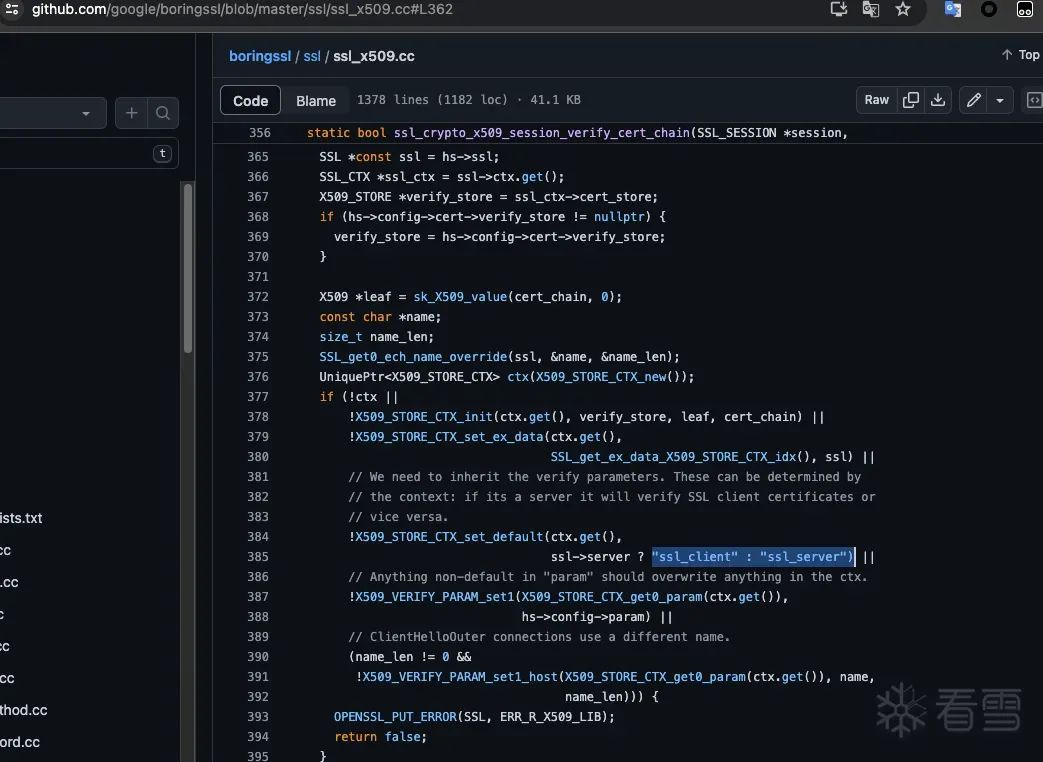
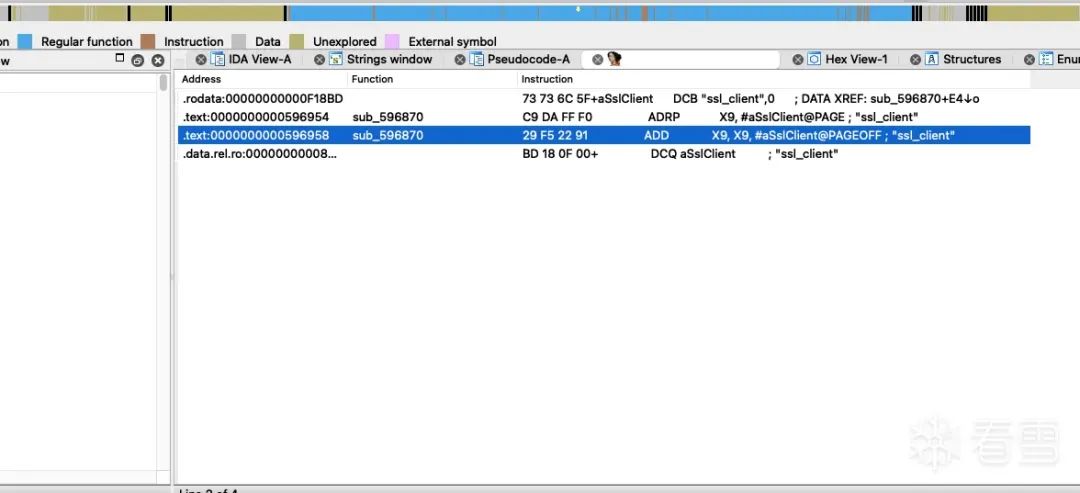
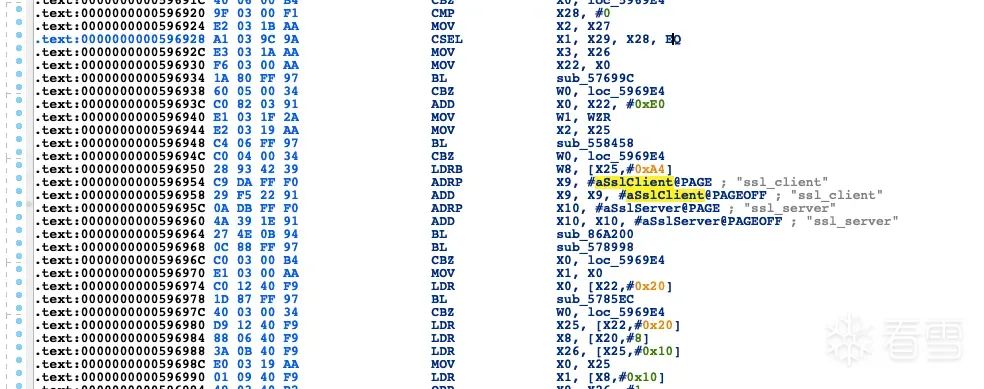
搜索ssl_client:
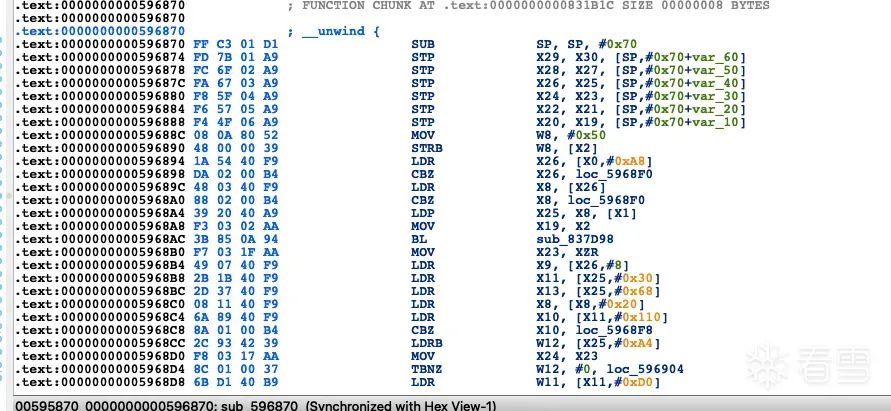
照例往上找:
然后就找到了这些:
.text:0000000000596870 FF C3 01 D1 SUB SP, SP, #0x70
.text:0000000000596874 FD 7B 01 A9 STP X29, X30, [SP,#0x70+var_60]
.text:0000000000596878 FC 6F 02 A9 STP X28, X27, [SP,#0x70+var_50]
.text:000000000059687C FA 67 03 A9 STP X26, X25, [SP,#0x70+var_40]
.text:0000000000596880 F8 5F 04 A9 STP X24, X23, [SP,#0x70+var_30]
.text:0000000000596884 F6 57 05 A9 STP X22, X21, [SP,#0x70+var_20]
.text:0000000000596888 F4 4F 06 A9 STP X20, X19, [SP,#0x70+var_10]
.text:000000000059688C 08 0A 80 52 MOV W8, #0x50
.text:0000000000596890 48 00 00 39 STRB W8, [X2]然后写脚本:
function hook_ssl_verify_result(address) {
Interceptor.attach(address, {
onEnter: function(args) {
console.log("Disabling SSL validation")
},
onLeave: function(retval) {
console.log("Retval: " + retval);
retval.replace(0x1);
}
});
}
function hookFlutter() {
var m = Process.findModuleByName("libflutter.so");
var pattern = "FF C3 01 D1 FD 7B 01 A9 FC 6F 02 A9FA 67 03 A9 F8 5F 04 A9 F6 57 05 A9 F4 4F 06 A9 08 0A 80 52 48 00 00 39";
var res = Memory.scan(m.base, m.size, pattern, {
onMatch: function(address, size){
console.log('[+] ssl_verify_result found at: ' + address.toString());
// Add 0x01 because it's a THUMB function
// Otherwise, we would get 'Error: unable to intercept function at 0x9906f8ac; please file a bug'
hook_ssl_verify_result(address.add(0x01));
},
onError: function(reason){
console.log('[!] There was an error scanning memory');
},
onComplete: function() {
console.log("All done")
}
});
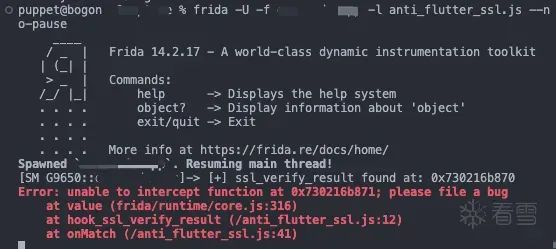
}然后发现报错了:
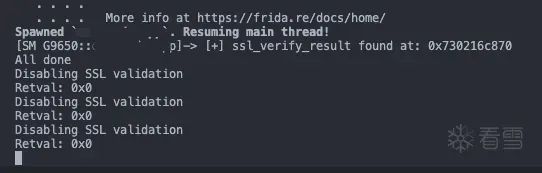
把hook_ssl_verify_result(address.add(0x01))改为hook_ssl_verify_result(address)就可以正常使用了:
3 参考资料
- https://www.jianshu.com/p/ada10d2976f2
- https://mp.weixin.qq.com/s/pXpfXK-Ez0n70f3bqFuuFg
- https://bbs.kanxue.com/thread-261941.htm
- https://blog.nviso.eu/2019/08/13/intercepting-traffic-from-android-flutter-applications/
以上四篇文章均是和flutter证书校验相关。